Encryption - The Invisible Shield Protecting Our Digital World
In today’s hyper-connected world, nearly everything we do—banking, messaging, shopping, working—happens online. But with convenience comes risk. Cyber threats, data breaches, and identity theft are constantly evolving. That’s where encryption steps in as a powerful defense mechanism.
What is Encryption?
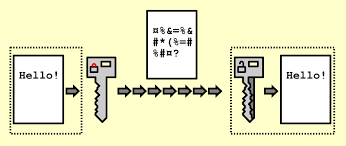
Encryption is the process of converting readable data (called plaintext) into an unreadable format (called ciphertext) using a mathematical algorithm and a key. Only authorized parties with the correct key can convert it back to its original form.
Think of encryption like locking your valuables in a safe. Without the key, the contents remain secure and inaccessible.
How Encryption Works
At its core, encryption relies on algorithms and keys:
- Symmetric Encryption: Uses the same key to encrypt and decrypt data.
- Asymmetric Encryption: Uses a pair of keys—a public key (to encrypt) and a private key (to decrypt).
Common encryption standards include AES (Advanced Encryption Standard) and RSA (Rivest–Shamir–Adleman).
Encryption may seem like magic—turning readable text into gibberish—but underneath, it’s all math, logic, and carefully designed systems. Let’s break it down step by step in a way that’s both practical and technically insightful.
The Core Idea
At its simplest, encryption does this:
- Plaintext + Algorithm + Key → Ciphertext
Ciphertext + Key → Plaintext
- - Plaintext: Original readable data
- - Ciphertext: Encrypted unreadable data
- - Algorithm: Mathematical function
- - Key: Secret value controlling the transformation
👉 The key is what makes encryption secure—not the secrecy of the algorithm.
Symmetric Encryption (One Key System)
In symmetric encryption, the same key is used for both encryption and decryption.
🔁 Process
- You take plaintext
- Apply an algorithm (e.g., AES) with a secret key
- Produce ciphertext
- Receiver uses the same key to decrypt
🧠 Conceptual Example
1
2
3
4
5
6
7
8
9
10
11
Plaintext: HELLO
Key: 3
Encrypted (Caesar Cipher):
H → K
E → H
L → O
L → O
O → R
Ciphertext: KHOOR
Inside AES (Advanced Encryption Standard)
AES is one of the most widely used encryption algorithms today.
⚙️ What Happens Internally?
AES works on fixed-size blocks (128 bits) and performs multiple rounds of transformations:
Each round includes:
- SubBytes: Substitutes bytes using a lookup table
- ShiftRows: Rearranges rows of data
- MixColumns: Mixes data across columns
- AddRoundKey: Combines data with part of the key
🔄 Simplified Flow
1
2
3
4
5
6
7
Plaintext Block
↓
Initial Key Addition
↓
Multiple Rounds of Transformation
↓
Final Ciphertext
👉 These repeated transformations create strong confusion and diffusion, making patterns impossible to detect.
Asymmetric Encryption (Two Key System)
Instead of one key, asymmetric encryption uses:
- Public Key (shared with everyone)
- Private Key (kept secret)
🔁 Process
- Sender encrypts data using the recipient’s public key
- Only the recipient’s private key can decrypt it
📦 Analogy
- Public key = open padlock anyone can use
- Private key = the only key that can unlock it
Hybrid Encryption (Best of Both Worlds)
In real systems (like HTTPS), both symmetric and asymmetric encryption are used together.
🌐 Example: HTTPS Connection
- Your browser connects to a website
- Website sends its public key
- Browser generates a random symmetric key
- Browser encrypts that key using the public key
- Server decrypts it using its private key
- Both now share a symmetric key for fast communication
👉 This approach is:
- Secure (thanks to asymmetric encryption)
- Fast (thanks to symmetric encryption)
Encryption Modes (Why AES Alone Isn’t Enough)
AES doesn’t just run by itself—it uses modes of operation.
Common Modes:
- ECB (Electronic Codebook) ❌ insecure (patterns leak)
- CBC (Cipher Block Chaining) ✅ better
- GCM (Galois/Counter Mode) ✅ modern & secure
Why Modes Matter
Without proper modes:
- Identical plaintext blocks → identical ciphertext
- Attackers can detect patterns
👉 Modes fix this by introducing randomness and chaining.
Initialization Vectors (IVs)
An IV (Initialization Vector) is random data added before encryption.
Purpose:
- Ensures the same plaintext encrypts differently each time
- Prevents pattern recognition attacks
Example:
1
Same password → different ciphertexts each time
👉 IVs are not secret, but they must be unique.
Hashing vs Encryption
These are often confused but serve different purposes:
| Feature | Encryption | Hashing |
|---|---|---|
| Reversible | ✅ Yes | ❌ No |
| Use Case | Protect data | Store passwords |
| Example | AES, RSA | SHA-256, bcrypt |
👉 Passwords should always be hashed, not encrypted.
Key Management (The Hardest Part)
Encryption is only as strong as how you manage keys.
🔑 Key Challenges:
- Secure storage
- Safe distribution
- Rotation (changing keys regularly)
- Revocation if compromised
🧠 Rule of Thumb:
If someone gets your key, encryption is useless.
Entropy & Randomness
Strong encryption depends on randomness.
- Weak randomness = predictable keys
- Predictable keys = broken security
Example:
- ❌ password123
- ✅ x9$K!pL2#vQ8
Real-World Example: Sending a Secure Message
Let’s walk through a simplified real-world flow:
- Alice wants to send Bob a message
- Bob shares his public key
- Alice:
- Generates a random AES key
- Encrypts message with AES
- Encrypts AES key with Bob’s public key
- Bob:
- Decrypts AES key with his private key
- Uses AES key to decrypt message
👉 This is how secure messaging apps work behind the scenes.
🛠️ Practical Encryption Examples
Below are real-world code examples showing how you might implement encryption in a project.
1. Symmetric Encryption (AES) in Python
This example uses the cryptography library to encrypt and decrypt data using AES.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
from cryptography.fernet import Fernet
# Generate a key (store this securely!)
key = Fernet.generate_key()
cipher = Fernet(key)
# Encrypt data
plaintext = b"Sensitive data"
ciphertext = cipher.encrypt(plaintext)
print("Encrypted:", ciphertext)
# Decrypt data
decrypted = cipher.decrypt(ciphertext)
print("Decrypted:", decrypted.decode())
✅ Use case: Encrypting files, database fields, or API secrets.
2. Password Hashing (Not Encryption) in Node.js
Passwords should not be encrypted—they should be hashed.
1
2
3
4
5
6
7
8
9
10
11
12
13
const bcrypt = require('bcrypt');
const password = "mySecurePassword123";
// Hash password
bcrypt.hash(password, 10, (err, hash) => {
console.log("Hashed:", hash);
// Verify password
bcrypt.compare(password, hash, (err, result) => {
console.log("Match:", result);
});
});
✅ Use case: User authentication systems.
3. Asymmetric Encryption (RSA) in Python
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
from cryptography.hazmat.primitives.asymmetric import rsa, padding
from cryptography.hazmat.primitives import serialization, hashes
# Generate keys
private_key = rsa.generate_private_key(public_exponent=65537, key_size=2048)
public_key = private_key.public_key()
message = b"Secret message"
# Encrypt with public key
ciphertext = public_key.encrypt(
message,
padding.OAEP(mgf=padding.MGF1(algorithm=hashes.SHA256()),
algorithm=hashes.SHA256(),
label=None)
)
# Decrypt with private key
plaintext = private_key.decrypt(
ciphertext,
padding.OAEP(mgf=padding.MGF1(algorithm=hashes.SHA256()),
algorithm=hashes.SHA256(),
label=None)
)
print("Decrypted:", plaintext.decode())
✅ Use case: Secure key exchange, encrypted communication.
4. Encrypting Data in a Web App (JavaScript - Browser)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
async function encryptData(data, password) {
const enc = new TextEncoder();
const keyMaterial = await crypto.subtle.importKey(
"raw",
enc.encode(password),
"PBKDF2",
false,
["deriveKey"]
);
const key = await crypto.subtle.deriveKey(
{
name: "PBKDF2",
salt: enc.encode("salt"),
iterations: 100000,
hash: "SHA-256"
},
keyMaterial,
{ name: "AES-GCM", length: 256 },
false,
["encrypt"]
);
const iv = crypto.getRandomValues(new Uint8Array(12));
const encrypted = await crypto.subtle.encrypt(
{ name: "AES-GCM", iv },
key,
enc.encode(data)
);
return { encrypted, iv };
}
✅ Use case: Encrypting sensitive data before sending it to a server.
5. Encrypting Environment Variables (Node.js)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
const crypto = require('crypto');
const algorithm = 'aes-256-cbc';
const key = crypto.randomBytes(32);
const iv = crypto.randomBytes(16);
function encrypt(text) {
const cipher = crypto.createCipheriv(algorithm, key, iv);
let encrypted = cipher.update(text, 'utf8', 'hex');
encrypted += cipher.final('hex');
return encrypted;
}
function decrypt(encrypted) {
const decipher = crypto.createDecipheriv(algorithm, key, iv);
let decrypted = decipher.update(encrypted, 'hex', 'utf8');
decrypted += decipher.final('utf8');
return decrypted;
}
✅ Use case: Protecting API keys and configuration secrets.
Key Benefits of Encryption
1. Data Security
Encryption protects sensitive information from unauthorized access. Even if data is intercepted, it cannot be read without the proper key.
Example: Your online banking details remain safe even if hackers capture the transmission.
2. Privacy Protection
Encryption ensures that personal communications and data remain confidential.
Example: Messaging apps use end-to-end encryption so only you and the recipient can read the messages.
3. Protection Against Cyber Attacks
Cybercriminals often target unencrypted data because it’s easy to exploit. Encryption adds a strong layer of defense.
Benefit: Even in the event of a breach, encrypted data is largely useless to attackers.
4. Secure Online Transactions
Encryption enables safe financial transactions over the internet.
Example: HTTPS websites use encryption to protect credit card details and login credentials.
5. Data Integrity
Encryption helps ensure that data has not been altered during transmission.
Result: You can trust that the information you receive is exactly what was sent.
6. Compliance with Regulations
Many industries require encryption to meet legal and regulatory standards.
Examples:
- Healthcare (protecting patient records)
- Finance (securing transactions and client data)
7. Trust and Reputation
Organizations that use strong encryption build trust with their users.
Impact: Customers are more likely to engage with platforms they believe are secure.
8. Protection of Intellectual Property
Businesses rely on encryption to safeguard proprietary data, trade secrets, and innovations.
Example: Companies encrypt internal communications and files to prevent leaks.
Real-World Applications of Encryption
- Messaging Apps: Secure conversations with end-to-end encryption
- Email Services: Protect sensitive communications
- Cloud Storage: Keep files safe from unauthorized access
- E-commerce Platforms: Secure customer data and transactions
- Virtual Private Networks (VPNs): Encrypt internet traffic for privacy
Challenges of Encryption
While encryption is powerful, it’s not without challenges:
- Key Management: Losing a key can mean losing access to data
- Performance Overhead: Encryption can slow down systems slightly
- Complex Implementation: Requires expertise to deploy correctly
The Future of Encryption
As technology evolves, so do encryption methods. Emerging trends include:
- Quantum-resistant encryption to prepare for quantum computing threats
- Zero-knowledge systems that enhance privacy
- Wider adoption of end-to-end encryption across platforms
🔐 Best Practices for Using Encryption
- Never hardcode keys in your codebase
- Use environment variables or secret managers
- Rotate keys regularly
- Use strong, modern algorithms (AES-256, RSA-2048+)
- Prefer established libraries over custom implementations
- Always use HTTPS for web applications
⚠️ Common Mistakes to Avoid
- ❌ Using outdated algorithms (like MD5 or SHA-1)
- ❌ Storing passwords in plaintext
- ❌ Reusing encryption keys improperly
- ❌ Ignoring proper key storage
🧩 Final Takeaway
Encryption isn’t just scrambling text—it’s a layered system involving:
- Algorithms
- Keys
- Randomness
- Protocols
- Secure implementation
When all these pieces work together correctly, encryption becomes one of the most powerful tools for protecting information in the digital age.
🔐 Encryption works not because it hides secrets—but because it makes breaking them practically impossible.
Get in Touch
Have suggestions, feedback, or specific topics you’d like us to cover? Don’t hesitate to reach out:
- 📧 Email: okelo2014@gmail.com
- 🐦 Twitter: @KnightLord_
- 📸 Instagram: i_am.shawn_
- 📱 WhatsApp: +254743198855
Thank you for stopping by, and let the learning adventure begin! 🚀
Appreciation:
Thank you for being a part of this journey. Keep the flame alive. Here’s to more learning and growth together!